 Vikas Maurya
Vikas Maurya
 Vikas Maurya
Vikas Maurya
Specializing in logic flaws, authentication bypasses, and business logic vulnerabilities across modern web applications. No scanners — just deep manual analysis and creative thinking.
I'm Vikas Maurya — known online as vikas0vks. I'm an independent security researcher focused exclusively on black-box testing of production web applications.
My approach is simple: I don't rely on automated tools. Instead, I reverse-engineer how developers think — mapping workflows, tracing state transitions, and identifying the assumptions baked into business logic. The vulnerabilities I find are the ones that scanners can't detect.
From authentication flows to payment systems, I specialize in finding high-impact flaws in critical infrastructure — the kind that get classified as Critical and High severity.
Recognized on Google's official Bug Hunters platform for identifying security vulnerabilities in Google products. Listed on the public leaderboard — ranked by reward total.
Verify on Google →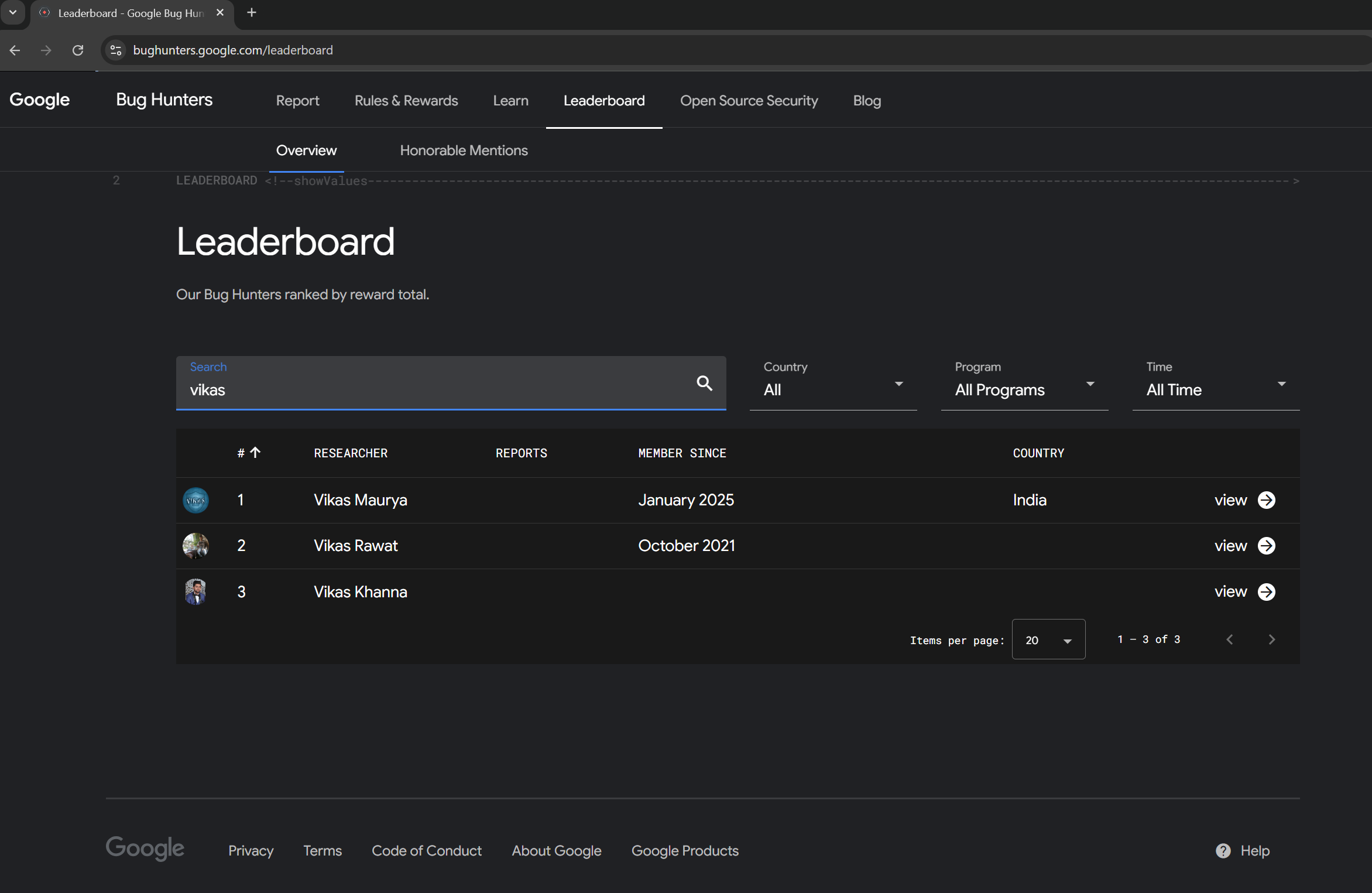
Listed on OZiva's Responsible Disclosure Program page for identifying and responsibly reporting critical security vulnerabilities in their platform. One of only 12 researchers recognized.
Verify on OZiva →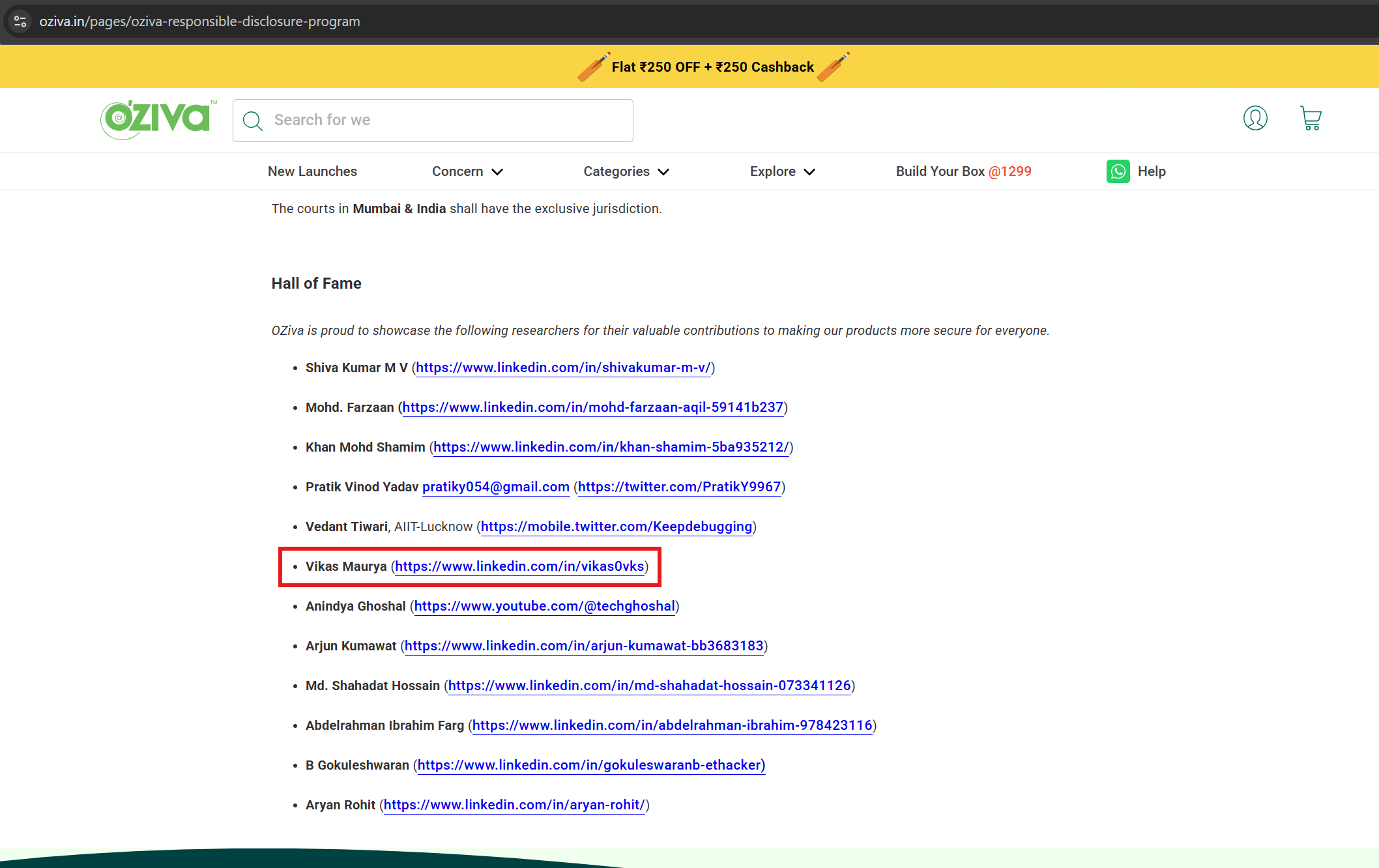
Across multiple platforms — authentication bypasses, IDORs, payment logic flaws, and business logic vulnerabilities.
Every vulnerability reported ethically through official channels. No data exposure. No unauthorized access. Full coordination with security teams.
Studying HackerOne reports, CVE advisories, and patch analysis daily to stay ahead of the curve.
I categorize every feature across 8 domains — identity, resources, authorization, billing, notifications, search, integrations, and state transitions. Nothing gets overlooked.
Happy paths, inverse operations, rate limits, state changes, cleanup logic — I map the complete lifecycle of every request before testing anything.
"Accounts must have at least one org." "Email is always verified first." "Users follow the linear flow." I find these hidden rules — then I break them.
Race conditions on cleanup handlers, state transition abuse, timing windows in async operations, bulk vs single-operation code paths — tested methodically, reported with full reproduction steps.
Looking for a security researcher for your platform? I'm available for private bug bounty programs, security assessments, and vulnerability research engagements.